Introduction to Computer Information Systems/Internet
Evolution of the Internet
[edit | edit source]
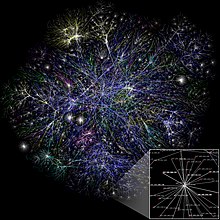
The internet has changed dramatically since its first incarnation. In 1969 the U.S. department of defense created ARPANET.[1] The original concept of this project was to connect researchers located in different places to be able to communicate and collaborate from far distances. The fear of nuclear attack was very prevalent at this time, so the team also wanted to make a network that could still operate after a nuclear attack. Therefore creating many different fail safes, and alternative routes for packet sending was necessary. As this project grew, more and more people gained access to the internet and began shaping it to what we know today. As we have described before, everyone who uses the internet is called an internet user. For these users to obtain access to the internet, you must go through an ISP (internet service provider.) Side note, while the internet is not owned by any one company or government, it is most assuredly not free. It costs money to build, run, and maintain the servers that bring you the funny cat videos.
Internet 2 is an amalgamation of different leaders in the field of academia, technology, industry, and government that formed together in order to collaborate on pioneering and innovative ideas that help advance education and research. They test new network applications and technologies using high-performance networks. Contrary to popular opinion, Internet 2 is not a gathering of minds who intend to replace the current Internet but congregate to ensure that the future Internet will be capable of operating with today's engineering. Internet 2 is currently being upgraded to 8.8 terabytes! This will aide in the ability to offer advanced telemedicine and long distance learning opportunities across connected countries through its network.[2]

The World Wide Web
[edit | edit source]The World Wide Web is different from the Internet. The Internet started out being used more by private industry and people, such as scientists, schools, and the government. The public did not use it for the most part because it was complicated and you had to have a computer to access it, which not everyone could. In 1989, Tim Berners-Lee came up with the World Wide Web and thought it would be a great way to organize information and replace the Internet. Although the Internet still exists and still exists today, the World Wide Web was a great tool for researchers at the time. The World Wide Web is not owned by a business or individual, but the Web is owned by it. The Web consists of things like HTML, URLs, and HTTP. HTML stands for Hyper Text Markup Language and is used to format documents on the Web. URLs are Uniform Resource Locators, which most of us are familiar with when we type in a Web site address. Finally, HTTP is the Hypertext Transfer Protocol. This is what allows people to click on a hyperlink and be redirected to that particular location. The World Wide Web has changed the way how school teach, businesses operate, and the way ordinary people access organized information.[3] Images and documents are now more readily available, and research and entertainment sites can now be found in one place.[4]
Using the Internet
[edit | edit source]Getting Set Up To Use The Internet
[edit | edit source]
Almost every household has access to the internet; therefore, it is important to know how to have access to the world wide web. There are five basic steps to set up an internet connection which consist of the following:
- One must connect the hardware. Different hardware and software contain directions in setting up. Use the directions to set up these systems.
- The internet needs a wireless connection or an Ethernet cable before it can go online. Therefore, the computer owner must make this connection.
- The computer owner must connect to the default IP address. The IP address usually consists of eight numbers, and it is broken up occasionally by periods.
- It is the internet's server's responsibility to show the computer owner how to actually establish the connection. One must then set up a name and password for security purposes.
- Save the settings, and the internet light will turn green to indicate one is online.[5]
Different Internet Connections
[edit | edit source]There are many different kinds of internet connections. A few of these connections consist of wireless, broadband, and dial-up. Wireless is a router or a network that connects to a hot spot. A broadband is connected directly to a broadband modern, and one needs a user name and password to connect. A dial-up is used remotely via a telephone line.[6] Different types of internet connections come with their own pros and cons and it is important to choose one that will work well with your lifestyle and your wallet.
Dial-up
[edit | edit source]Dial-up connection requires a phone line to function. Because of this, people cannot be using the phone and the internet at the same time. When connecting to the internet via dial-up, the computer tries to connect through the phone line and causes dial-tones and many numerous sounds to emit from the modem. Dial-up is also the slowest form of internet connection and has a maximum speed of 56 kilobits per second. It is also the most archaic type of internet connection and only about 3% of Americans are still using it.[7][8]
Wi-fi Hotspots
[edit | edit source]`Wi-fi hotspots are another form of internet connection in which a wireless access point, such as a router, has a direct connection to the internet and allows people to connect wirelessly through the use of wi-fi. Although they aren’t used very much at home, wi-fi hotspots are often used at locations such as restaurants, hotels, and airports. Many restaurants such offer free wi-fi to entice customers, while others have a fee for using their internet.[9]
Broadband over Fiber
[edit | edit source]
A new technology called broadband over fiber (BoF) is a direct connection option for internet access. Internet service providers are starting to adopt this new technology and sell it for a fee.[10] For example, Verizon's version of broadband over fiber is called fiber-optic service (FiOS). FiOS, in particular, is able to provide services such as telephone, television, and internet. BoF is advertised on Verizon's FiOS webpage as a network that, "provides bandwidth to meet today's digital demands and the possibilities of tomorrow."[11] This statement is probably used because BoF's data transfer speeds are much faster than other services. In fact, with fiber-optic cabling, data transfer can travel at the speed of light. One drawback of BoF is that it is very expensive. In order to create a fiber-optic network, you must invest a lot of money in constructing an essential infrastructure. Another negative with broadband over fiber is that the cables are very sensitive. This means that cables can not be installed on telephone poles or underground. Cables must be installed above ground, usually in piping, so that the cables are protected from bending and shifting. BoF is practical and efficient for small networks due to less complex construction of infrastructure. This being said, the United States probably won’t have nation wide BoF networks.[12]
Selecting an ISP
[edit | edit source]There are many different Internet Service Providers, some of the most popular include Comcast, AT&T, Verizon, and Time Warner Cable.[13] When you choose an ISP, there are many factors to take into consideration. Some of those factors include price, type of internet connection you want, speed, customer support, types of devices you use, and cancelation policies.[14]

Some internet service providers, such as Verizon and Google, are now starting to offer fiber-optic internet connections. Fiber-optics allows unsurpassed connection speeds, both upload, and download. Fiber-optic internet connections employ Fiber-optic cables that transfer large amounts of data through hundreds of stands of glass or plastic based on entirely light based, optical technology. The technology has existed for many years, but many may have begun to hear that it has become more commonly available over the recent years. After implementing fiber-optics in commercial internet service packages, Internet Service Providers are now able to confidently boast connection speeds exceeding 100 gigabits per second, speeds that are much more desirable to many households as well as businesses.[15] Fiber optic networks are, to no surprise, very expensive.
Large-scale ISPs may not be ready to spend hundreds of millions, if not billions, on citywide fiber networks, so the technical transition to fiber-optic is a lengthy process. Google alone spent over 80 million dollars to reach 150,000 households with their fiber-optic connections. Only a small handful of cities currently have the luxury of a fiber-optic connection, and it may take some years before the technology is available to a majority of households.[16]
Searching the Internet
[edit | edit source]Search Engines
[edit | edit source]
Search sites are websites that are specifically created to help search the Internet. Examples include, “Google,” “Bing,” “Yahoo! Search,” and “Ask.com.” There are also many other not as well known search sites. Search sites generally use a search engine, which is a program for the retrieval of data from a database or network. A search engine includes a spider, which goes to every page on every Web site that wants to be searchable and reads it. Then there is a program that creates an index from the pages that have been read. Then a program that receives your search request and compares it to the index, then gives you results.[17] Most search sites today are designed for keyword searches, which is when you type in keywords describing what you are searching for. A directory search is the other kind of search that some sites allow and it uses lists of categories instead of a search box.[18] Many search sites will also contain tools that can be used to find information. Many sites try to present their results as clearly as possible. They will also tend to make suggestions about things that are similar to what you searched that may help you find what you are looking for.[19]

When it comes to search sites, there are a few that almost everyone is familiar with. The common phrase, “Google It,” is an indication that Google has become a household name when it comes to search engines. Google boasts an astounding 1,100,000,000 monthly visitors. With numbers like that, it is easy to see why Google has become the household name for search engines. However, few are as familiar with some of the other search sites that are available today that provide the same kind of service that Google does. One of these lesser known search sites is Duck Duck Go. One of this site's great features is that it does not share any of its clients' data with other search sites which makes for less advertisement pop ups and stronger privacy for the user. This has appealed to more and more users after information surfaced that the U.S. has direct access to the servers of major search engine companies allowing the U.S. government to gain knowledge of exactly what people are searching for. This information inspired the founder of Duck Duck Go, Gabriel Weinberg, to start this company in 2008, to ensure the rights and privacy of its users. Gabriel Weinberg was quoted as saying, “Search data is arguably the most personal data people are entering into anything. You’re typing in your problems, your desires. It’s not the same as things you post publicly on social networks.” Duck Duck Go has is a great alternative to larger search engines and for users who really value their privacy.[20]

Search Strategies
[edit | edit source]
Searching for particular information can be fun but also can be very frustrating. Here are few different search strategies which can help to find the information needed, such as simple, complex, phrase, natural language and default Boolean Logic searching. Simple searching is the easiest method of using a search tool.[21] The user can type one or more key words (spelling counts) in the search box then click on the search button. Complex searching is using Boolean Logic[22] to improve search efficiency. The words such as AND, OR, and NOT are entered between keywords to refine the search. In phrase searching, a user should enclose quotation marks when searching for specific phrase. Most search engines like Google, Bing, and such recognize this protocol. Natural Language searching is allowing a user to type a sentence or question just the way he/she might like and the search tool will try to determine key words and locate pages based on these words. Default Boolean Logic searching allows a user to type key words as in simple search. Search tool, depends on its default, will use OR or NOT. If a user is tired of typing, she/he can click on the microphone icon in the Google app or Chrome’s search box to search by voice.[23]
Beyond Browsing and Email
[edit | edit source]Instant Messaging and Text Messaging
[edit | edit source]Communication is quite possibly the most important tool that humans can hone. While e-mails are a fast and environmentally-friendly method of Internet-based communication, there are two types of messaging that are faster and easier. These two types of messaging are: instant messaging and text messaging. Instant messaging, also referred to as chat, allows you to type out a message on your keyboard and then press 'enter' to have it sent immediately to the other party. Unlike emails, where you have to wait for the other person to be around at their computer to read the message, and THAT is assuming your email didn't get lost because of a faulty spam filter, IM's create a connection that is almost as good as being in the same room with the friend. To instant message a friend, you typically both need the same IM client, of which there are many free varieties such as AIM, MSN, YIM, and Skype.
Text messaging, which is also called SMS (Short Message Service), used to be the most popular means of speedy communication though it has been on the decline.[24] Text messaging allows users to send fast and typically short notes with their cellular phones. While text messaging used to be quite expensive, majority of cellular plans sold today include unlimited texting.[25] Text messages, like emails, need to be waited for and can sometimes not make it to the right place without a glitch. Instant messengers, however, tend to have a better track record.
Online Shopping: Amazon and More
[edit | edit source]
Online shopping is so convenient for many who are on the go. There are no hours of operation to abide by, no lines to wait in, and consumers do not even have to leave the comfort of their own home to get what they want. There are some downsides of online shopping, such as not being able to try on clothes to see if it is the right size. The largest online retailer is Amazon.com. Shoppers seems to go-to website for all online shopping needs. The retailer started as an online book store, but now offers purses, electronics, movies, music, and even sports equipment, just to name a few. Sellers can create accounts fairly easy and try to sell their goods. Buyers need to be the cautious ones and look into the reviews to see who they are buying from. One advantage of shopping with Amazon is that they have an A-Z guarantee that helps the buyers resolve conflict with the sellers.[26] Amazon expanded their services to include areas such as Amazon Art, Amazon Instant Video, Amazon Prime, Amazon Local, Amazon Wireless, Amazon Fresh, and Amapedia. One controversy that comes up with Amazon.com, as well as online shopping, is that consumers are not paying their true county sales tax. Instead they are paying the sales tax that Amazon collects.To challenge Amazon, Google has decided to start to expand its e-commerce role. Google wants to compete with amazon and their ability to sell merchandise around the world. Google is allowing consumers to search for something and Google would tell them if there is somewhere nearby to purchase that item. It is a great retaliation against amazon. They would charge $95 a year or $10 a month, or pay $4.99 per order. Google is also offering overnight shipping.[27]
Online Banking
[edit | edit source]Online Banking has become increasingly popular in this tech-savvy generation. Most banks now allow transactions to be done online through their website or through phone apps. While some people question the security of making transactions online, the biggest advantage is that online banking is very convenient. People can set up accounts through a few simple steps, can make transactions between different accounts they have, transfer money, make payments on credit cards, and more. Some only-online banks have formed and are gaining popularity because they have less fees and thus are cheaper. Some banks try to offer deals with higher yield to make online banking more appealing. Lastly, it is handy to have 24/7 access to speedy transactions, which traditional banks cannot offer. Online banking did have a shaky start, but now it is growing quickly.[28] According the Bankrate website, 65% of consumers use online banking.
Pros and Cons
[edit | edit source]In the last few years, online banking has become increasingly mainstream. For some, it is the new norm, as having to make daily or weekly trips to the bank can be both unpleasant and inefficient. For the most part, online banking is advantageous -- and though the pros certainly outweigh the cons, no system is flawless.
First, an obvious pro is convenience. An ability to pay the majority of bills online, whether it is through a checking, savings, money market account, etc. is something that is necessary in our fast-paced, demanding world. Many creditors offer an automatic plans to ensure customers are not charged penalties if they forget to pay a bill. In addition, there is also mobile capability. Most banks feature mobile-friendly websites that allow customers to bank on-the-go. The applications banks offer are typically free, and are being implemented with new features all the time in an effort to expand availability to smartphone users. Lastly, the ease of navigation is comparable to that of any other website. To prevent or assist with issues, most banks have 24-hour live customer service or e-mail customer service.
The most significant con to online banking is security, with computer hacking and identity theft being such widespread problems. Despite the best security measures, there is always risk that someone, somewhere will be able to gain access to your bank account and/or sensitive information. Another concern is transaction issues. There are some aspects of banking that should be done behind a teller’s desk instead of a monitor or screen. Depositing cash, certain types of international deals, and similar difficulties may be challenging to address or solve via the internet. Another, less threatening issue for those who frequently make impulse purchases or budget poorly is a lack of money management, as instant access to a balance can precipitate irresponsibility. [29]
Social Media
[edit | edit source]

Besides texting, instant messaging, and online shopping, there are hundreds of other things you can use the Web for. One of the main things people use it for today is social media. Things from Facebook and Twitter to email and online newspapers are all forms of social media, or sites used to share information to groups of people over the Internet. The problem with the huge explosion that has been the beginning of the social media era is that it is becoming increasingly difficult to believe information posted online. The Internet has evolved so much that now we are able to even perform video and telephone functions through it. Sites like Skype are taking advantage of this technology. According to the FCC (Federal Communications Commission) the technology used by Skype, Vonage, and other similar Companies is called VoIP. They define this technology as one “that allows you to make voice calls using a broadband Internet connection instead of a regular (or analog) phone line”.[30] Essentially, performing telephone functions through the Internet is VoIP. Social Media has seemingly encompassed the younger generations of today; while it has been slower to catch on with the older generations, it is something that has been increasing over time. Skype had recently acquired a newer company called Qik and plans on dominating the new way for people to communicate using mobile video messaging. Skype Qik is supposed to be very simple, and it is exactly like texting but all video. A person can send a Qik video to anyone and they do not even have to have the app. These conversations are asynchronous and Skype Qik is a great idea for communication since things like Facetime have been a big trend. The thing with Facetime though is that someone has to answer the phone and both people need to use it at the same time; with Skype Qik people have the ability to have that type of video interaction but at no specific time. Skype Qik was developed by Microsoft, and is available on a PC or Mac, and for the iPhone, Android, or Windows phone.[31]
Another popular social media app is Snapchat. This app allows people to send pictures, videos, and texts, just like other apps, but the catch is that once the picture/video/text is opened, it disappears after the set amount of time and cannot be see again. Snapchat has many features which make Snapchat photos and videos more fun and interesting than on other apps. Such features include filters, different text fonts, and the ability to draw on the pictures/videos with different colors. In addition to these original features, Snapchat has added a feature called “My Story” where users can create a chain or video of multiple pictures and videos combined. This story is not sent to one specific person, rather any of the user’s friends can see it; the set time in this feature determines how long the picture shows in the “slide show” and the story is available for only twenty-four hours. The latest feature is “geolocation” which can give you the time, weather, miles per hour, or other site-specific filters based on your location.[32]
RSS and Podcasts
[edit | edit source]
First invented by Netscape, Really Simple Syndication (RSS) is an online tool designed to quickly distribute new articles and other content when it is changed or added to. The reason for its invention was because it was an easy way for Netscape to share headlines and stories from other sites, and automatically add it to their own. To help people keep updated on their favorite websites, RSS uses an XML code that constantly scans a website and then broadcasts those updates to all the subscribers through its RSS feed. Subscribing to an RSS feed—usually for free—is fairly simple, as all one has to do is sign up with a feed aggregator, which will store all of one’s RSS subscriptions, and then click the subscribe link on the associated Web page. Finally, its feed content will automatically be added to their browser feed list, similar to the Favorites Feed list in Internet Explorer. For better accessibility for today’s evolving generation, RSS feeds can also be delivered to mobile phones and maybe even directly to televisions sometime in the future. [33]
Another simple way to gather useful information from the Web is a Podcast, which is simply a recorded audio or video file that can be downloaded from the Web. Derived from the combination of the words “broadcasting” and “iPod,” podcasting is a form of audio broadcasting, which can be listened on one’s iPod. However, this is not a limitation since podcasts also be listened to on computers via the Windows Media Player or iTunes, or smartphones. The difference between podcasting and simply downloading and listening to music online is the fact that with podcasting, files come to you through syndication, instead of the other way around. Much like the blogs and websites mentioned previously, podcasts can be subscribed to in order to download new podcasts whenever they become available. [34]
Online Testing
[edit | edit source]Online testing is becoming a new alternative for taking tests in this technology-based world that we live in nowadays. Online tests can be used for both objective tests, like multiple choice or true/false, or performance-based tests, like a concussion test. The state of Washington started using online testing in the spring of 2010 to administer tests of math and science for grades 3-8.[35] This testing format creates more options for a teacher’s curriculum. Usually, one or two days are necessary to complete a test in class, but with an online test, no class days are taken up. This allows for the teacher to either go more in-depth on topics, allow for more Q&A during class room time to make sure his or her students understand the material, more time to prepare for an online test day, or it allows for more material to be covered. All of these options are great for the education system because students gain more knowledge from their tuition. One problem with online testing is security. How would a teacher know if the right student is taking the test, if the student is looking online or using another person to help them? To overcome this obstacle, technology companies are creating devices like the Securexam Remote Proctor system that takes a 360-degree image of the room and uploads it to a server where the teacher of the class can view it. All in all, online testing is the wave of the future for the education system with testing.
Blogs, Wikis, and Other Types of Online Writing
[edit | edit source]
A blog is a Web page that contains short, frequent updated entries in chronological order, typically as a means of expression or communication. Blogs can be written by anyone, including ordinary people, celebrities, or even experts of certain fields. As blogs become more and more popular, commercial advertising begins to be commonly seen on more of the popular blogs. Some of the most popular blogs are websites that offer information or helpful tips to their readers. For example, as of October 2014, the top three most popular blogs are: Huffington Post, TMZ, Business insider.[36] Another form of online writing, most often used for education purposes, is the wiki. Wikis are a way of creating and editing collaborative Web pages quickly and easily. Unlike a blog, wikis are meant to be edited by anyone, not just the owner of the typed information. One of the largest wikis is Wikipedia(Wikibooks is an example of a wiki too). While wikis are helpful and collaborative, erroneous information can be added intentionally. As a result, it is recommended to be careful when fully trusting a wiki page. Another type of online writing is an e-portfolio. An electronic portfolio is a collection of an individual's work accessible through a website. Today. e-portfolios are commonly linked to student-related information, such as resumes, papers, or projects.
Online Gaming
[edit | edit source]
Everywhere you look, young people are using smartphones, notebook computers, iPads, etc. Often, they are not just using these devices for school research, homework, or studying. Young people can be seen playing games on computing devices as young as 3 years old. Online gaming is a rapid habit that is starting from a very young age. Often, the habit carries into the young adult years for many individuals. Nowadays, there are whole web sites whose sole purpose is hosting games that can be played online. Online games can be played alone or with other individuals who are also online. The games that are designed to be played by multiple players are called online multiplayer games. Some examples of online multiplayer games are Doom, EverQuest, Final Fantasy, City of Heroes, and World of Warcraft. Also, gaming devices, such as, PlayStation 3, Xbox 360, and Wii, are deigned to be Internet-enabled so they can be connected to the Internet to play with other players. Online gaming has also been associated with Internet addiction. An article about online gaming addiction in The Kernel, states that often individuals are playing online games 12 hours a day. The article explains that individuals that develop online gaming addiction lose jobs and loved ones, have withdrawal symptoms, and develop migraines and back problems. The article states that it is a very real problem and will potentially continue to grow in the population as the Internet becomes more readily available to more and more people.[37]
Video Chatting
[edit | edit source]
Video calls have played a major part in science fiction for decades. They were a major part of the film 2001: A Space Odyssey, and many other films and TV shows of that genre. Now, video chatting capabilities are found as standard on most desktops, and mobile devices. On of the most well known programs, and the program that pioneered video chatting, is Microsoft’s Skype. In recent years, Skype has been joined by Apple’s Facetime, and a video chat program embedded in Google Hangouts. Skype is compatible with Microsoft, Mac, and Linux computers, and there is and app for mobile devices. Facetime however, is only available on Apple devices, although the company has promised to make it compatible with other devices at some point. Google Hangouts, being a part of Google online app suite, is available as long as the user is able to access the Internet. There are other free source programs, but these three are the most common and the most trusted by security programs. Some free source options that now have become very popular is Facebook's Messenger App and WhatsApp; these are both available for download on most smartphones. Video chatting was touted as a futuristic ideal, but in recent years, this has not held true. Video chatting use has decline in favor of texting and online testing apps. These may be the future as opposed to video chatting. [38]
Censorship and Privacy
[edit | edit source]Censorship
[edit | edit source]Censorship is the control of the information distributed within a society and has been a sense of dictatorships throughout time. It’s the suppression of offensive expressions that are used for when people want to provoke their personal political or values to another group. Typically now censorship is filtered by the government to control the information that is given to the public. Censorship by the government is typically unconstitutional because of the freedom of speech and is highly fought against in the First Amendment. However, other countries routinely censor information and have strict rules against their citizens posting information that the authorities do not like, for example, China and North Korea. On another note, when individuals in US are on strike or boycott an event they are protected by the First Amendment which can be dangerous but they are still known to be protected. Some private censorship campaigns are best countered by groups and individuals speaking out and organizing in defense of the threatened expression.[39][40]
Fighting Internet Censorship
[edit | edit source]
Internet users who live in countries where the government tries to block or inhibit Internet use can still sometimes access material that is supposed to be forbidden. One way to do this is via a proxy, where Internet connectivity is routed through another server. If, for example, Facebook is blocked, an Internet user can use connect to a proxy server that, in turn, connects to Facebook, giving the user access to Facebook without directly connecting to it.[41] A VPN (Virtual Private Network) can also be used to bypass such laws; however, different providers provide different layers of security (some do not log any information, some providers encrypt whatever is sent etc), and it is generally better to pay for one than try to use a free VPN. There is also a browser dedicated specifically to Internet activity known as TOR for "The Onion Router", which proves multiple layers of encryption, like layers of an onion, as the data people are submitting or accessing is routed through multiple different 'nodes' and encrypted in between each one. The idea is that this will provide total anonymity, so that people cannot be tied to their access of or posts on certain websites. While it is sometimes given a negative connotation as a tool only for criminals, TOR is actually incredibly useful for people in countries whose governments are trying to oppress their citizens' freedoms of speech and press.[42] In short, while it is not easy or necessarily safe for people in these nations to access everything they should be able to access on the Internet, it is possible, and there are some means of circumventing government censorship of the Internet, which is not always holeproof.
Web Browsing Privacy
[edit | edit source]
Privacy is of great importance to all users of the Internet. According to Wikipedia, internet privacy involves the right or mandate of personal privacy concerning the sorting, repurposing, provision to third-parties, and displaying of information pertaining to oneself via the Internet.[43] This has been a subject of concern for decades. For example, one article that addresses the potential implications of privacy and computer dates back to 1965.[44] While it is certain that privacy can be infringed, a simple awareness of how exactly certain processes, like using a search engine, interact with a user can be help deal with some of these concerns.
When one uses a search engine, such as Google, small files known as cookies are created to help identify preferences for the user. This enables a more accurate and quicker response when beginning a new session. To put this into context, cookies can help retrieve information like what was in a shopping cart for a previous session. However, third-party cookies can be more of an issue to some. Companies use these cookies to target advertisements towards users depending on their browsing patterns. Using the Internet Options in Internet Explorer (for Windows) can help one decide what types of cookies can be allowed as well as delete all cookies off the hard drive.
A more serious threat to internet privacy is spyware, which refers to any software that is installed without knowledge of the user that obtains information about that user through an Internet connection. The degree to which these programs can cause harm range from simple annoyances (e.g. setting a homepage to something else) to full-scale threats on system integrity (e.g. rewriting the Windows registry to restrict the user from changing the homepage back to its original state).
Adware, while related to spyware, is less harmful. Adware is usually installed alongside other software, and this leads to advertisements that appear on-screen. This can be installed without prior knowledge during the installation of another program by not reading the licensing agreements that came with the program. Therefore it is important to read carefully the agreement to ensure unwanted software is kept away from the computer.

In order to prevent personal information from being compromised and to keep your computer and internet running smoothly there are several precautions that should be taken to ensure that your web browsing experience is a safe and private one. Perhaps the easiest method to do this is by activating private browsing on your internet browser application. Once turned on the browser can not save any files or data to your local machine, including cookies, cache, and history. If you are using regular browsing, these files can still be deleted through your browser or another application. Disposing of these files ensures that online sites cannot track your activity on the web. You can also use programs to ensure that you are not being targeted for certain advertisements because of your browsing history, a common occurrence in the modern marketing age. To be very anonymous on the internet, a Tor network can be setup that encrypts the data you are sending so that your IP address is not compromised.[45] Another similar method is proxies, which are intermediates that receive and deliver information requested. This keeps your personal computer information private as the server is technically the one making the request, not you.[46]
E-mail Privacy
[edit | edit source]
It is extremely important to always make sure that any important or confidential information being shared over the Internet is being done in a private and confidential way. One of the unfortunate downfalls to everything being done electronically today is that we lose a sense of privacy. Things are much easier to attain on the Internet, and sadly there are hackers out there who spend their time trying to break into and gain access to this confidential information. If you are going to send important information electronically, it is necessary that you send it in an encrypted message. Encrypted messages make it so that others cannot hack into your e-mails and read what you are saying. One of the more recent controversies with privacy in e-mailing has to do with Google mail. Google has come out saying that they should be able to read the information sent by any of its Gmail users. People find issue with this because they are gaining personal and confidential information that individuals do not want out there. The purpose of sending a specific email to a specific individual is so that it can be done in privacy, with the hopes that only that recipient will receive it. However, today this is unfortunately not the case, and if you are going to send mail electronically, one needs to proceed with caution.[47]
Review
[edit | edit source]Review Definitions
[edit | edit source]Mobile Phone:A phone such as a cellular, or satellite phone that uses a wireless network.
Cell Phone:A mobile phone that communicates via a cellular network.
Satellite Phone:A mobile phone that communicates via satellite technology.
Dual-Mode Phone:A mobile phone that can be used with more than one communications network, such as with both a cellular and Wi-Fi network.
Global Position System (GPS:A system that uses satellites and a receiver to determine the exact geographic location of the receiver.
Videoconferencing:The use of computers, video cameras, microphones, and networking technologies to conduct face-to-face meetings over a network.
Telecommuting:The use of computers and networking technology to enable an individual to work from a remote location.
Telesurgery:A form of robot-assisted surgery in which the doctor's physical location is different from the patient's physical location and the doctor controls the robot remotely over the Internet or another network.
Telemedicine:The use of networking technology from the location of the doctor to provide medical information and services to the patient in a different location.
Wireless Network:A network in which computers and other devices are connected to the network without physical cables; data is typically sent via radio waves.
Star Network:A network that uses a host device connected directly to several other devices.
Bus Network:A network consistent of a central cable to which all network devices are attached.
Mesh Network:A network in which there are multiple connections between the devices on the network so that messages can take any of several possible paths.
Personal Area Networks (PANs):A network that connects an individuals's personal devices that are located close together.
Local Area Networks (LANs):A network that connects devices located in a small geographical area, such as within a building.
Wide Area Networks (WANs):A network that connects devices located in a large geographical area.

Intranet:A private network that is set up similar to the Internet and is accessed via a Web browser.
Extranet:An intranet that is at least partially accessible to authorized outsiders.
Virtual Private Networks (VPNs):A private, secure path over the Internet that provides authorized users a secure means of accessing a private network via the Internet.
Analog Signal:A type of signal where the data is represented by continuous waves.
Digital Signal:A type of signal where the data is represented by 0s and 1s.
Serial Transmission:A type of data transmission in which the bits in a byte travel down the same path one after the other.
Parallel Transmission:A type of data transmission in which bytes of data are transmitted at one time, with the bits in each byte taking a separate path.
Twisted-Pair Cable:A networking cable consisting of wire strands twisted in sets of two and bound into a cable.
Coaxial Cable:A networking cable consisting of a center wire inside a grounded, cylindrical shield, capable of sending data at high speeds.
Fiber Optic:A networking cable that utilizes hundreds of thin transparent glass fibers over which lasers transmit data as light.
Cellular Radio:A form of broadcast radio designed for use with cellular telephones that broadcasts using antennas located inside honeycomb-shaped cells.
Microwave Station:An earth-based device that sends and receives high-frequency, high-speed radio signals.
Communications Satellite:An earth-orbiting device that relays communications signals over long distances
Infrared (IR) Transmissions:A wireless networking medium that sends data as infrared light waves.
TCP/IP:A networking protocol that uses packet switching to facilitate the transmission of messages; the protocol used with th Internet.
Ethernet:A widely used wired LAN networking standard.
Wi-Fi:A facility allowing computers, smartphones, or other devices to connect to the Internet or communicate with one another wirelessly within a particular area.
WiMax:An emerging wireless networking standard that is faster and has a greater range than Wi-Fi.
Wi-Fi Direct:A standard for connecting Wi-Fi devices directly, without using a router or an access point
Bluetooth:A networking standard for very short-ranged wireless connections; the devices are automatically connected once they get within the allowable range.
Ultra Wideband (UWB):A networking standard for very short-range wireless connections among multimedia devices.
WirelessHD:An emerging wireless networking specification designed for connecting home consumer devices.
Wireless USB:A wireless version of USB designed to connect peripheral devices.
TransferJet:A networking standard for very short=range wireless connections between devices; devices need to touch in order to communicate.
Network Adapter:A network interface, such as an expansion card or external network adapter.
Network Interface Card (NIC):An expansion card through which a computer can connect to a network.
Modem:A device that enables a computer to communicate over analog networking media, such as connecting to the Internet via telephone lines.
Switch:A device used to connect multiple devices on a single (typically wired) network; forwards packets to only the intended recipient.
Router:A device that connects multiple networks together; routes packets to their next location in order to efficiently reach their destination.
Wireless Access Point (WAP):A device on a wireless network that connects wireless devices to that network.
Wireless Router:A router with a built-in wireless access point; most often used to connect wireless devices to a network and an Internet connection and often contains a built-in switch.
Bridge:A device used to bridge or connect two LANs; most often used to connect wired devices wirelessly to a network.
Repeater:A device on a network that receives a signal and retransmits it.
Range Extenders:A repeater for a wireless network.
Antennas:A device used for receiving or sending radio signals; often used to increase the range of a network.
TOR: "The Onion Router" a browser dedicated specifically to Internet activity which proves multiple layers of encryption, like layers of an onion, as the data people are submitting or accessing is routed through multiple different 'nodes' and encrypted in between each one.
Review Questions
[edit | edit source]References
[edit | edit source]- ↑ wiki: ARPANET
- ↑ http://www.internet2.edu
- ↑ http://webfoundation.org/about/vision/history-of-the-web/
- ↑ http://www.nethistory.info/History%20of%20the%20Internet/web.html
- ↑ http://www.wikihow.com/Set-Up-an-Internet-Connection
- ↑ http://windows.microsoft.com/en-us/windows-vista/what-are-the-different-internet-connection-methods
- ↑ http://www.cnet.com/news/3-percent-of-american-adults-still-cling-to-dial-up-internet/
- ↑ http://www.packetworks.net/blog/internet-connection-types
- ↑ http://en.wikipedia.org/wiki/Hotspot_(Wi-Fi)
- ↑ Understanding Computers 14th Ed. by Deborah Morley & Charles Parker
- ↑ http://www.verizon.com/home/fios/
- ↑ http://www.wisegeek.com/what-are-the-pros-and-cons-of-fiber-optic-broadband.htm
- ↑ http://www.practicalecommerce.com/articles/3225-20-Top-Internet-Service-Providers
- ↑ http://www.easyt1.net/blog/10-things-to-consider-when-choosing-an-internet-service-provider
- ↑ http://arstechnica.com/business/2014/04/one-big-reason-we-lack-internet-competition-starting-an-isp-is-really-hard/
- ↑ http://en.wikipedia.org/wiki/Fiber-optic_communication
- ↑ http://www.webopedia.com/TERM/S/search_engine.html
- ↑ http://www.webopedia.com/TERM/K/keyword_search.html
- ↑ http://webaim.org/techniques/sitetools/
- ↑ http://www.dailymail.co.uk/news/article-2360059/DuckDuckGo-little-known-search-engine-refuses-store-data-users-doubles-web-traffic-amid-NSA-tapping-scandal.html
- ↑ https://www.bcps.org/offices/lis/models/tips/searchstrategies.html
- ↑ http://www.webopedia.com/TERM/B/Boolean_logic.html
- ↑ https://support.google.com/websearch/answer/134479?hl=en
- ↑ http://blog.brosix.com/why-instant-messaging-is-now-more-popular-than-sms/
- ↑ Cell Phone Plan Cost
- ↑ http://www.ioba.org/newsletter/archive/8%284%29/toolbox2.php
- ↑ http://www.dailyherald.com/article/20141014/business/141019213/
- ↑ http://www.bankrate.com/finance/checking/pros-cons-online-checking-accounts-1.aspx
- ↑ http://www.nasdaq.com/article/the-pros-and-cons-of-online-banking-cm386361
- ↑ http://transition.fcc.gov/voip/
- ↑ http://www.theverge.com/2014/10/14/6973625/skype-qik-video-messaging-features
- ↑ http://mashable.com/2014/08/13/snapchat-tips-and-tricks/
- ↑ http://www.wisegeek.com/what-is-rss.htm
- ↑ http://www.entrepreneurs-journey.com/230/what-is-a-podcast/
- ↑ https://www.k12.wa.us/Assessment/StateTesting/OnlineTesting.aspx
- ↑ http://www.ebizmba.com/articles/blogs
- ↑ http://theweek.com/article/index/255964/the-psychology-of-video-game-addiction
- ↑ http://www.howtogeek.com/186267/the-3-easiest-ways-to-video-chat-online-or-on-the-go/#
- ↑ http://gilc.org/speech/osistudy/censorship/
- ↑ https://www.aclu.org/free-speech/censorship
- ↑ http://www.rfa.org/about/help/web_access.html
- ↑ https://www.torproject.org/
- ↑ https://en.wikipedia.org/wiki/Internet_privacy
- ↑ http://www.multicians.org/fjcc6.html
- ↑ http://www.cnet.com/how-to/five-smart-ways-to-keep-your-browsing-private/
- ↑ https://en.wikipedia.org/wiki/Proxy_server
- ↑ http://www.foxnews.com/tech/2013/09/05/google-seeks-to-dismiss-gmail-privacy-lawsuit-says-it-has-right-to-scan/