Steganography/Covers
Text
[edit | edit source]Undetectability: very small 1
Bit rate: poor 2
Resistance to modification: average 3
Methods
[edit | edit source]Line shift coding
[edit | edit source]This method moves whole lines of text about 0.003 inches up or down
J. T. Brasie proved with his research that even after printing, copying and re-scanning 10 times, the message is still extractable. For this reason, it is a way to protect copyrights.
Whitespace coding
[edit | edit source]it's family steganographic methods, which consist in hiding the text with white characters, eg. spaces.
Whitespace is text composed only of spaces, tabs, carriage returns or line feeds. In a web browser, any amount of whitespace in between words is treated the same as a single space. Whitespace at the start and end of elements and outside elements is completely ignored.[1] Encoding a hidden message in the number and kinds of "redundant" space messages does not change how a web page is displayed in a web browser.[2][3]
Extra newlines are invisible in the web browser, but may be noticed in a text editor, so some systems add only tabs and spaces (not adding any newlines).[4]
Encoding a hidden message in the spaces and tabs, but only at the ends of lines, makes the message invisible even in a text editor.[5]
Character coding
[edit | edit source]Character coding hides the secret message by modifying features of the cover text.
Feature coding
[edit | edit source]It boils down to finding the character of letters or entire words and using it to hide information. Such a feature can be, for example, the length of the "petioles" of letters, thanks to which the system is again obtained for binary coding of the stegotext.
Letter coding
[edit | edit source]- Stego type: private key
This technique was used, among others by German intelligence services during World War II. Modern example:
WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues
Let us take an example. To extract this message, it is enough to read only the first letter from each word of the stegosystem:
uti nsa im cu si
Syntactic method
[edit | edit source]This method of hiding the text takes advantage of another weakness of the human mind - the tendency to make mistakes. For example, it can enter a certain number of punctuation errors into the text. They should not be noticed because most people make them. Unfortunately, the difficulty will appear when the text is corrected. You can use this method in a private list or on the online forum, but the problem starts when you want to use this method, for example, in an article of a magazine or other text that will be corrected and should be written without error.
Semantic method
[edit | edit source]This is one of the most effective methods of hiding secret information in the text. It's about using synonyms to encode secret information. For example, the words: large and its great synonym are given the appropriate value: 0 and 1. Thanks to this, having a sufficiently large carrier, you can encode stegotext. Undoubtedly, the amount of secret information hidden by this method is quite severely limited.
Aesop language
[edit | edit source]Aesopian language is communications that convey an innocent meaning to outsiders but hold a concealed meaning to informed members of a conspiracy or underground movement. For instance, if Person X is known for exposing secrets in an organization, the organization leaders announce that "any members who have dirty talking habits will be dealt with" to warn Person X. It refers to the ancient Greek fabulist Aesop. Example
it's raining
in language freemasonry warning that there is a profane (worldly) in their group, at which one should not talk about matters of the Order.
Detection of such things are far beyond any power of modern AI and generally is outside computational capabilities of snooping agencies. In a way they represent much more complex Turing test then traditional Turing test.
Social stenography
[edit | edit source]communities with social or government taboos or censorship, people use cultural steganography—hiding messages in idiom, pop culture references, and other messages they share publicly and assume are monitored. This relies on social context to make the underlying messages visible only to certain readers. Example:
On 4chan was banned services like motheress.com and other. Using the properties of portal links (content is available via hex code). Instead of throwing the whole link, just upload ID. the method used is as follows:
Porn - motherless
image - imgur
text - pastebin
video - youtube (as except, use this base64)
On polish portal chomikuj.pl is here an unwritten tradition, file wasn't deleted from the cloud, it should be "protected" with the password of the user's name.
Emoticons
[edit | edit source]This approach hides the secret message (s) using emoticons, with each emoticon assigned to a single letter.
Secret message:
HELLO
embed:
B-) =-0 0:-) 0:-) :-X
Table:
| Emoticons | Alphabets/Numbers Assigned |
| :-) | A |
| :-( | B |
| :-P | C |
| =-O | D |
| :-* | F |
| :O | G |
| B-) | H |
| :-$ | I |
| :-! | J |
| :-[ | K |
| O:-) | L |
| :-\ | M |
| :’( | N |
| :-X | O |
| :-D | P |
| o_O | Q |
| :-/ | R |
| x-( | S |
| :-| | T |
| <3 | U |
| :-V | V |
| XD | W |
| :-Q | X |
| :-@ | Y |
| :-C | Z |
| :-O | 1 |
| :-S | 2 |
| :-B | 3 |
| :-# | 4 |
| X( | 5 |
| 0:) | 6 |
| @-}-- | 7 |
| :*) | 8 |
| -:) | 9 |
| >:) | 0 |
this method it's similar to increase in entropy as like Leetspeak, padonki or even polish script is call unofficial poke writing
Sudoku
[edit | edit source]This technique hides a secret message (s) in a 9x9 Sudoku puzzle.
embed
Solve the sudoku puzzle no.40 000:005:962 103:070:040 500:082:700
Software
[edit | edit source]spamminic it's proof-of-concept generator which transform hidden text on text appar spam. Example:
hidden text:
uti nsa im cu si
result:
Dear Business person ; Your email address has been submitted to us indicating your interest in our newsletter ! This is a one time mailing there is no need to request removal if you won't want any more ! This mail is being sent in compliance with Senate bill 2716 ; Title 1 , Section 303 . This is not multi-level marketing . Why work for somebody else when you can become rich inside 86 days ! Have you ever noticed society seems to be moving faster and faster and the baby boomers are more demanding than their parents . Well, now is your chance to capitalize on this . WE will help YOU sell more and decrease perceived waiting time by 200% . The best thing about our system is that it is absolutely risk free for you . But don't believe us . Mr Ames who resides in Florida tried us and says "My only problem now is where to park all my cars" . We assure you that we operate within all applicable laws ! So make yourself rich now by ordering immediately ! Sign up a friend and you'll get a discount of 10% . Cheers ! Dear Internet user ; Thank-you for your interest in our publication . If you are not interested in our publications and wish to be removed from our lists, simply do NOT respond and ignore this mail . This mail is being sent in compliance with Senate bill 2116 ; Title 4 , Section 302 ! This is not a get rich scheme . Why work for somebody else when you can become rich in 41 DAYS . Have you ever noticed people love convenience plus most everyone has a cellphone . Well, now is your chance to capitalize on this . We will help you deliver goods right to the customer's doorstep & turn your business into an E-BUSINESS . The best thing about our system is that it is absolutely risk free for you ! But don't believe us . Ms Anderson of Hawaii tried us and says "I was skeptical but it worked for me" ! We are licensed to operate in all states ! We BESEECH you - act now ! Sign up a friend and you get half off ! God Bless .
Photos
[edit | edit source]Undetectability: Very large 5 (changes in the image not detectable to the human eye) [6]
Bit rate: good 4 [7]
Resistance to modification: Very good 5 [8]
Flickr also has a unique 1TB disk - no current cloud provider provides so much storage space. Unfortunately, there is a limitation of file types only for photo and video. However, thanks to steganographic techniques, this is not a problem.
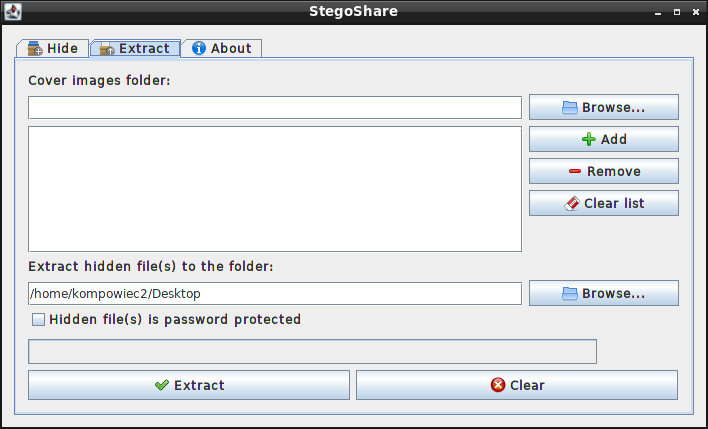
- Download and running the StegoShare program

- In the "hide" tab, select the folder with photos (Cover images folder)
- In "File to hide" of course, we select the file that we want to hide (in this case, the RAW file)
- Optionally, you can choose the AES encryption by entering the password below
- "keep cover image original filenames" means leaving the original file names
- To reverse the process, go to the "extract" tab and indicate the folder we just created.
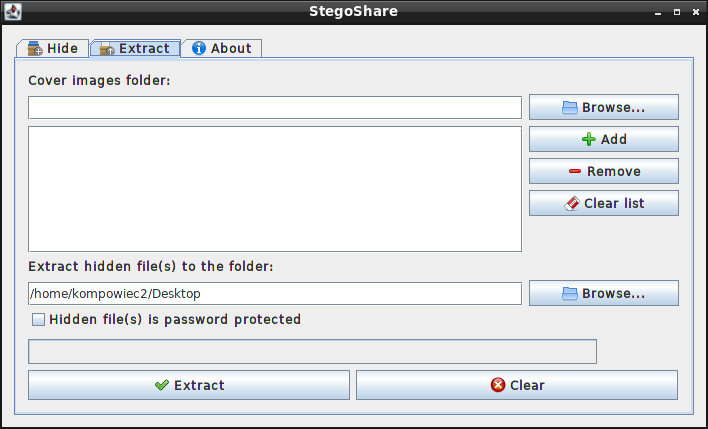
- later choose the place where he will unpack.
Stegoshare is very good program embedded files from cover however file can't infinitely large - supported only 2 GB. Second problem, stegoshare usage algorithm LSB which is quite easy to detect and in each algorithm will be much slow for huge files. How to fix? use compressed? Nope - it's very simple, can embbeded in one pic .torrent file! Steghide usage graph which is harder to be detected and thanks to usage bittorrent protocol We aren't limited by file sizes.
Thirdly, the idea of merging .torrent files and media files brings a positive side effect to StegTorrent, making it useful even without any privacy and security concerns. While choosing media files as cover data, it is possible to pick such files which have a descriptive and/or demostrative function regarding the target of the torrents. For instance, rather than having the poster of a movie and a torrent for it's trailer, why not just embed the torrent into the poster image? - stegtorrent
GIF
[edit | edit source]- Undetectability: Very large 5 (every pixel of the Gifshuffled image has an identical color to the corresponding pixel in the original image)
- Bit rate: ?
- Resistance to modification: ?
Unlike most steganography tools, Gifshuffle creates an image that is pixel-for-pixel identical in color to the original image. GIF files have a colormap of up to 256 different colors. The order of that colormap has no effect on the image that is displayed. Gifshuffle re-orders the colormap into one of the 256! possible orders (about 2^1683 possible orders), in order to encode a short message of about 1683 bits (210 bytes) of information.[9]
Video
[edit | edit source]Undetectability: Very large 5 [10]
Bit rate: Excellent 6
Resistance to modification: Good 4 [11]
Development of the above technology, allows you to put the most data from all containers. One of the representatives is OpenPuff that supports the largest number of containers, including video files.

Audio
[edit | edit source]Bit rate: medium 3
Undetectability: poor 2
Resistance to modification: weak 2
DeepSound
Executable files
[edit | edit source]HTML
[edit | edit source]HTML, which is visible by examining the document source. HTML pages can contain code for extra blank spaces and tabs at the end of lines, and colours, fonts and sizes, which are not visible when displayed.[2][12]
Other
[edit | edit source]- ↑ "How whitespace is handled by HTML, CSS, and in the DOM".
- ↑ a b Iman Sedeeq; Frans Coenen; and Alexei Lisitsa. "A Prediction Model Based Approach to Open Space Steganography Detection in HTML Webpages".
- ↑ Ishita Bajaj; R. K. Aggarwal. "RSA Secured Web Based Steganography Employing HTML Space Codes And Compression Technique".
- ↑ "Whitespace Steganography Conceals Web Shell in PHP Malware"
- ↑ Matthew Kwan. the steganographic nature Of whitespace (SNOW)
- ↑ 1 LSB technology is relatively easy to detect
- ↑ 1 more data is needed to hide more data
After StegoShare, the size of hidden files is about 40% of the size of the original file. - ↑ -0.5 method susceptible to lossy compression, however, it can be omitted to some extent by using a digital watermark
- ↑ "GIF colourmap steganography"
- ↑ -1 Detection techniques are the same as for photos
- ↑ -2 any modification will result in data loss!
- ↑ Chaitali Patel; Nimisha Patel. "A Suvey Paper on Information Hiding on WebPages"