Radium SmartChain/Linux Mint Hack
On February 20, 2016 the Linux Mint website was hacked. The hackers were not only able to access the Mint mirrors to replace the iso files, but also got into the website and replaced the check-sums on the downloaded isos. What this means is if you downloaded their iso on the day it was hacked, even verifying the download would have returned that it was the appropriate file since the incorrect check-sum was being used for verification.
How could this issue have been avoided?
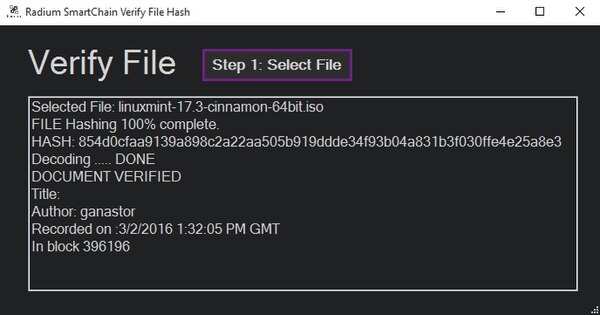
[edit | edit source]With Radium Smart-Chain technology! With the ability to record a file's check-sum directly into the blockchain, the sha256 hash would have been forever recorded and impervious to external manipulation. This technology seeks to allow users the ability to quickly verify the integrity of open-source and shared files within a single user-friendly application as demonstrated below:
1) The first step would be done by the creator of the original file being shared. This user would record the files check-sum on the Smart-Chain during the process of making it publicly available for download.
2) The second step is done by any user wanting to download the shared file in question. Much like the first step, the user simply identifies the file through the Smart-Chain and receives a confirmation that the file is intact and unchanged if the check-sums check out.
Additional Radium Smart-Chain Functionality and Cyber-Security Implications
[edit | edit source]Along with recording file check-sums, the SmartChain also has the ability to record text notes. What this means is the sha256 check-sum text file located at http://mirrors.kernel.org/linuxmint/stable/17.3/sha256sum.txt could have been permanently recorded with no chance of a man-in-the-middle attack being able to replace the text file from the mirror website!
With the ability to verify hashes in the SmartChain instead of relying solely on potentially compromised websites, users will not only be able to avoid infecting their machines, but they will also be able to pro-actively combat compromised files leading to a much safer inter-netting experience.