Communication Networks/Network Topologies
Topologies
[edit | edit source]The shape of a network, and the relationship between the nodes in that network is known as the network topology. The network topology determines, in large part, what kinds of functions the network can perform, and what the quality of the communication will be between nodes.
Common Network Topologies
[edit | edit source]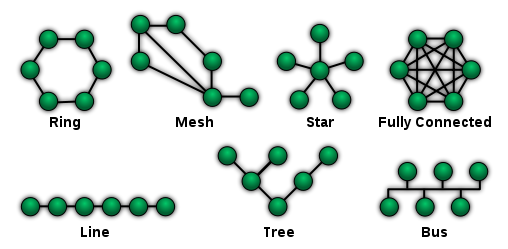
Star Topology
[edit | edit source]A star topology creates a network by arranging 2 or more host machines around a central hub. A variation of this topology, the star ring topology, is in common use today. The star topology is still regarded as one of the major network topologies of the networking world. A star topology is typically used in a broadcast or SIMO network, where a single information source communicates directly with multiple clients. An example of this is a radio station, where a single antenna transmits data directly to many radios. If there are n number of nodes in a star topology connection, the connecting lines between the nodes should be n - 1.
Tree Topology
[edit | edit source]A tree topology is so named because it resembles a binary tree structure from computer science. The tree has a root node, which forms the base of the network. The root node then communicates with a number of smaller nodes, and those in turn communicate with an even greater number of smaller nodes. A host that is a branch off from the main tree is called a leaf. If a leaf fails, its connection is isolated and the rest of the LAN can continue onwards.
An example of a tree topology network is the DNS system. DNS root servers connect to DNS regional servers, which connect to local DNS servers, which then connect with individual networks and computers. For your personal computer to talk to the root DNS server, it needs to send a request through the local DNS server, through the regional DNS server, and then to the root server. This is a good example of a tree topology.
Ring Topology
[edit | edit source]A ring topology (commonly known as a token ring topology) creates a network by arranging 2 or more hosts in a circle. Data is passed between hosts through a token. This token moves rapidly at all times throughout the ring in one direction. If a host desires to send data to another host, it will attach that data as well as a piece of data saying who the message is for to the token as it passes by. The other host will then see that the token has a message for it by scanning for destination MAC addresses that match its own. If the MAC addresses do match, the host will take the data and the message will be delivered. A variation of this topology, the star ring topology, is in common use today.
Mesh Topology
[edit | edit source]A mesh topology creates a network by ensuring that every host machine is connected to more than one other host machine on the local area network. This topology's main purpose is for fault tolerance, as opposed to a bus topology, where the entire LAN will go down if one host fails. In a mesh topology, as long as 2 machines with a working connection are still functioning, a LAN will still exist.
The mesh topology is still regarded as one of the major network topologies of the networking world.
Line Topology
[edit | edit source]This rare topology works by connecting every host to the host located to the right of it. Most networking professionals do not even regard this as an actual topology, as it is very expensive (due to its cabling requirements) and due to the fact that it is much more practical to connect the hosts on either end to form a ring topology, which is much cheaper and more efficient.
Bus Topology
[edit | edit source]A bus topology creates a network by connecting 2 or more hosts to a length of coaxial backbone cabling. In this topology, a terminator must be placed on the end of the backbone coaxial cabling. In Michael Meyer's Network textbook, he commonly compares this network to a series of pipes that water travels through. Think of the data as water; in this respect, the terminator must be placed in order to prevent the water from flowing out of the network.
Hybrid Topologies
[edit | edit source]A hybrid topology, which is what most networks implement today, uses a combination of multiple basic network topologies, usually by functioning as one topology logically while appearing as another physically. The most common hybrid topologies include star bus, and star ring.
Network Areas
[edit | edit source]Wireless networks do not have fixed topologies, so it doesn't make sense to talk about shape of these networks. Instead, other characteristics such as network size and node mobility are of primary importance.
Wireless networks and networking protocols can be divided up based on their intended range. Networks with smaller ranges have smaller power requirements and often have less noise to deal with. However, small networks are only able to communicate with small numbers of clients, compared with larger nodes. Increasing the number of clients in a network is often more useful, but more aggressive techniques need to be employed to prevent data collisions among multiple users in a large network.
Network Size Designations
[edit | edit source]- Personal Area Network (PAN)
- Extremely small networks, often referred to as "piconets" that encompass an area around a single person. These networks, such as Bluetooth, have a range of only 1-5 meters, and tend to have very low power requirements, but also very low datarates.
- Local Area Network (LAN)
- LAN networks can encompass a building such as a house or an office, or a single floor in a multi-level building. Common LAN networks are IEEE 802.11x networks, such as 802.11a, 802.11g, and 802.11n.
- Metropolitan Area Network (MAN)
- These networks are designed to cover large municipal areas. Data protocols such as WiMAX (802.16) and Cellular 3G networks are MAN networks.
- Wide Area Network (WAN)
- Wide-Area Networks are very similar to MAN, and the two are often used interchangeably. WiMAX is also considered a WAN protocol. Television and Radio broadcasts are frequently also considered MAN and WAN systems.
- Regional Area Network (RAN)
- Large regional area networks are used to communicate with nodes over very large areas. Examples of RAN are satellite broadcast media, and IEEE 802.22.
- Sensor Area Networks
- These networks are low-datarate networks primarily used for embedded computer systems and wireless sensor systems. Protocols such as Zigbee (IEEE 802.15.4) and RFID fall into this category.