Communications and Networking:Internet Security
Firewalls
[edit | edit source]
A firewall is a device or program that monitors and controls data traffic between the internet and a private network (such as your network at home). Every firewall can be customised and assigned rules which determine which data packets are allowed through from the internet and which are not.
Firewalls can also be used to block data from certain IP addresses, domain names or port numbers. Many firewalls also have the capability of being able to search individual packets for specific matches of text.
Packet filtering -
- When using the packet filtering method, the firewall analyses the packets that are sent from the internet against a set of filters (firewall rules) which determine whether or not the packet is allowed to go through.
Proxy server -
- Proxy servers prevent the user of a private network coming into direct contact with the computer that hosts a web page on the internet. This works by the proxy requesting the data from the internet and then passing it on to the private network user.
Encryption
[edit | edit source]Encryption is used to hide sensitive messages from illegitimate recipients by using encryption algorithms and an encryption key to convert plain text to cipher text, illegible to those without the encryption and decryption key. Private/Public key encryption is when both parties have a pair of keys, one private and one public. The Public Key is kept in the open freely usable by anyone as is the encryption algorithm, however the Private Key is kept hidden.
- A message encrypted with A's public key can only be decrypted with A's private key.
- A message encrypted with A's private key can only be decrypted with A's public key.
- A message encrypted with B's public key can only be decrypted with B's private key.
- A message encrypted with B's private key can only be decrypted with B's public key.
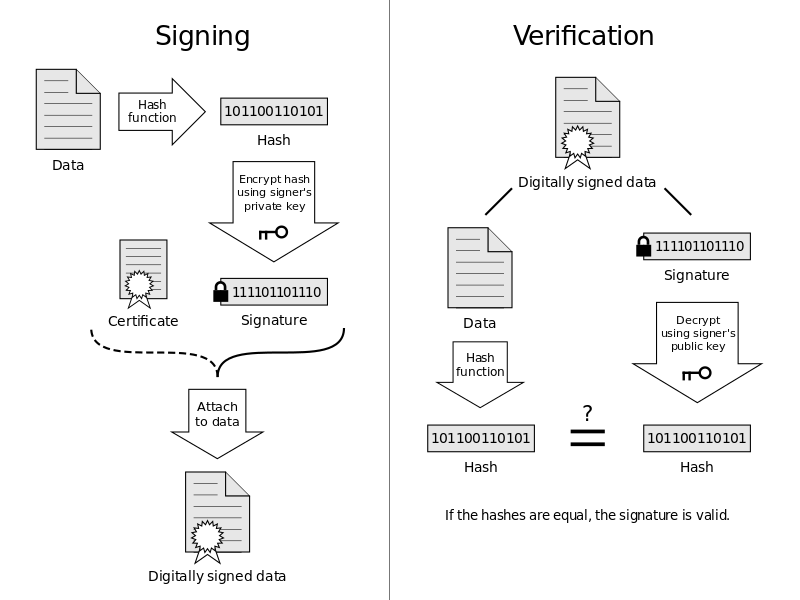
Digital signatures
[edit | edit source]Digital signatures are a way for the sender to prove to the receiver that the message did in fact originate from them. A digital signature is obtained through the following process:
| Processes required before A sends the message to B | Processes required to ensure the message is from A |
|---|---|
| Message is hashed to get a message digest. | B decrypts the message with B's private key. |
| The message digest is encrypted with A's private key, this then becomes the signature. | B decrypts the signature with A's public key to get the original message digest. |
| The signature is appended to the message. | The decrypted message is hashed again, reproducing the message digest. |
| The message is encrypted using B's public key. | The message has not been tampered with if the decrypted message digest is the same as the reproduced digest. |
| The encrypted message is sent to B. |
A Digital Certificate is a way of proving that the public key of the sender is authentic. Digital Certificates are only issued by a certification authority (CA). The certificates are encrypted into the message via the CA's private key, and can only be decrypted with the CA's public key.
Security Threats
[edit | edit source]There are a number to be aware of:
Viruses
[edit | edit source]A virus is a small computer program attached to another program or file and is intended to cause harm to a computer. The first step that a computer performs when the program is executed is to copy itself onto the disk and hide itself. After being copied onto the disk the virus can reside in memory and reconfigure the system so it causes problems such as displaying unwanted messages, destroying or corrupting files or even wiping the entire hard disk. Viruses tend to replicate themselves and also try to spread to other computers. Anti-virus programs are used to detect and remove these viruses. Nowadays web browsers have built-in virus scanners which scan files that are available for download.
Worms
[edit | edit source]A worm is a malicious program designed to replicate itself in an attempt to spread across a computer network such as the internet. The most significant difference between a worm and a virus is that a worm is a complete program on its own. Worms can disrupt network traffic and damage data.
Spam
[edit | edit source]Spam is the flooding of irrelevant unwanted message (silly pointless annoying messages) these can either be by email, SMS or instant messaging. Email spam is usually considered junk mail and millions of spam emails are sent every day. Text messaging spam is also used by companies to advertise themselves. Spam is considered to be disruptive and a waste of network bandwidth.
Phishing
[edit | edit source]Phishing is the act of deceiving a user to give sensitive information about themselves. This may happen by the use of phishing emails or even phishing sites, these look like the site the user is trying to access but are not, they are intended to capture information from the user. The term phishing comes from fishing, where instead of catching fish, information is caught.
Pharming
[edit | edit source]Pharming is technique used to redirect traffic from one website to another, Phishing and Pharming are used in conjunction. Pharming is the process of redirecting users to a different location so that a phishing technique can imitate and capture information about the user.
Computer Security Procedures
[edit | edit source]Authentication, Authorisation, Accounting.
Authentication
[edit | edit source]Verification of the user of the computer system. Forms of Authentication include passwords, biometric data, security tokens and digital signatures.
Authorisation
[edit | edit source]Specifying the access rights of different users to resources on a network.
Accounting
[edit | edit source]Keeping logs of user activity on a network.