Introduction to Computer Information Systems/Database
Database Definition and Examples[edit | edit source]

A database is a collection of data that is saved and organized to allow easy retrieval when needed. It is the collection of schemas, tables, queries, reports, views, and other objects. In order to maintain and access the database you will need a DBMS (database management system). This kind of system manages and protects data so that the database is safe and secure. Databases are not limited to only computers; in fact, a phone book is an example of a database.[1] All of the names alphabetized and each column has its own category. There is a column for your name, phone number, and possibly a street address. With a relational database, all of the data within the row can be pulled up when you are looking for the specific attribute.

There are a few advantages to using a database management system. On the plus side, it has the ability to control redundancy, the integrity of the information being stored can be maintained, it can restrict access, it can share data, and can backup/recover information. A database management system can counteract redundancy by compiling the information in one spot. The same way that you can't have two audio files with the same name and extension in a single folder, you can't have the same file in a single database. This controls and can increase storage space. The integrity of the information being stored can also be increased based on the specifications of the database developer. This means that the constraints on the information put into the database (which is determined by the developer) will keep the data stored accurate. If a database is only able to store pictures, for example, then a music file will be rejected ensuring that a picture will always be retrieved from the database with 100% accuracy. This is a very simple example to get the idea across as the constraints imposed by the developer can determine different things. Databases can also share data as well allowing a developer to build multiple applications off of one source of information rather than having to create new stored files. Databases can also backup and recover data. If a computer system fails during a long, complex update then the database can restore the files to the place in the update when it is becomes operational again.[2]

Primarily, databases are used for collecting data and organizing, one may wonder what instances this may be used for. Some examples of databases are Microsoft Excel or Access. For an example of what these databases could be used for we can go with a situation: you are having a wedding and need to make an invitation list. For a process like this, users can utilize Microsoft Excel because their database will not have many types of transactions and should not become too uncontrollable. However, if this were to happen, Access would be more compatible with the material needed. Access is basically just a more advanced version of Excel that is only needed for uncontrollable databases or ones that need to be directly linked to others in order to access information in a systematized way. Either database can help you make informed decisions and can also help you make sense of the data in different ways. The storage in Access is not repetitive so it can essentially save space and improve accuracy.[3] Access also has different templates to choose from so that you do not have to create a new database from scratch. There is also a relationship you can establish between the tables so that you can navigate easier. For creating a wedding invitation list: you can decide who to invite and who not to invite to the reception and put those people in separate tables.[4]

Databases are also important in businesses. Especially when it comes to keeping inventory. Databases can be used for controlling inventory as well as reducing the time, cost, and effort of inventory management. Controlling your inventory is essential in order to have good and efficient business. A database can provide an up-to-date picture of stock levels and products. It helps in maintaining that the stocks keep up with the demand of the consumers. It can be used to provide forecasts and trends of demand in order to adjust adapt to the change of the market and maximize profit. It also provides automation which improves productivity. It can update stock levels automatically as well as control stock to ensure products are always available for consumers. This automation frees up employees to do more productive things such as help out customers. Speaking of customers, they always order things and want them delivered on time and right away. Well a database can help in increasing and maintaining the efficiency of orders and deliveries. They help make it easier to place orders and find products. While these are also important in business they can be applied to any organization that may have inventory. An example of such would be libraries. With the millions of books that a library can potentially carry, a database is not only important but necessary.[5]
Who Uses Databases?[edit | edit source]

There are a number of individuals who create, use, manage, and secure database management systems. A database designer is responsible for designing a database. They work with people involved in the system development life cycle, such as systems analysts, to find out what kinds of data are needed and what relationships among the data should be studied, and they design the database based off of these. A database designer may also be referred to as a database architect, database engineer, or database analyst. Database developers create the database based on the work of the database designer, setting up its structure and user interface, typically with the use of the database management system. This may be the same as the database designer, and they work alongside the database programmer, who creates the programs necessary for the database to be developed. Database administrators, or DBAs, manage databases within an organization, maintaining them, monitoring user access to them, monitoring their performance, and performing backup. The users are the ones who actually "use" the database: they enter data into the database, update data within the database, and retrieve data from the database.[6]
Data Characteristics[edit | edit source]

Data is a collection of facts. It can be values, measurements, numbers, words, measurements, and observations. Many businesses would not be as successful without data.[7] A data has a hierarchy; this hierarchy is a systematic organization of data. Fields, records, and files are a part of the data organization. Product names or quantities are the lowest level of the hierarchy, and the database is the highest level of the hierarchy.[8] Also, the data definition consists of the following: name, data type, description, and properties. This describes the properties that go into a database. If a computer user wants to look up all of the data definitions for a database, he or she would look up the data dictionary. A few key terms a computer user should be aware of, concerning data characteristics, consist of data field, record, file, and database. A data field contains a single fact of an entity. A record is a collection of related fields. A file is an organization of related business records. The database is the place where files are integrated. The data characteristic key terms are essential to be aware of for businesses who use a database.
Data Organization[edit | edit source]

In order for a database to be efficient, its data must be organized in a fashion to make it easily and quickly accessible. This is called data organization. Data organization typically uses a primary key to identify where data is being stored. This allows for a specific record to be located efficiently. There are a few different methods that databases use in order to store and retrieve data efficiently. The two most common are Indexed Method and Direct Method. Indexed Method is the method in which a database uses an index to keep track of where data is stored within it. An index is a table that has the primary key as well as the location information for that key. Index organization allows for records to be looked up quickly and retrieve information from the database. Direct organization is faster than index organization. This is due to it using the key field and a mathematical formula called hashing algorithm to find where specific records are physically stored in the database. These systems are much harder to develop. They pave the way for an incident called collision, which happens when two or more records are assigned the same storage address. Some systems use both methods. The key field will first indicate where the record is located in the table, and then the hashing algorithm is used to find where the data is physically stored on the storage medium.[9]
The Data Dictionary[edit | edit source]
A data dictionary is a read-only set of tables that contain all data definitions in a database. The table structures are non-editable without a password. A password is needed to view or edit a table. The definitions included in the database include all of the following: tables, views, indexes, clusters, synonyms, sequences, procedures, functions, packages, triggers, and more. Keep in mind; the data dictionary does not contain any of the information located in the data tables, only the data about the tables. This specific data about the tables is otherwise known as metadata. The database dictionary includes information regarding how much space has been taken up by the schema objects and the amount of space that is left. [10] The information that is included in the database must be organized before put into the data dictionary. Data modeling, or putting a descriptive name to each data object, must be done for each independent object. Once that is done, the relationship of the data is described, along with the description of type of data. Type of data can include defining the object as text or an image. Once that is completed, the programmer must include a brief textual description regarding the data. [11]
Data Security and Privacy[edit | edit source]
Data security is a must-have, and is required by most industry, business and legal mandates. Data security is what protects data from being breached (eg seen by people who should not see it), so that the information it contains cannot be disclosed or leaked. Data security also ensures the integrity of the data, meaning that no unauthorized changes can be made to data, data structures, configuration files, or logs. Data security programs can keep track of the files and monitor the transferring of data to prevent unauthorized access and stop any possible intrusions from occurring.[12]
Because technology has developed so much over the years, more and more actions are taking place online through the internet, apps, or other networks. This has raised the issue of privacy, as personal and sensitive information is often held in the databases of many organizations (hospitals, insurance companies, jobs, health care companies, etc.). To help solve this, privacy laws have been made to determine how companies and individuals can have the ability to choose what information can be given to third parties and what cannot be given out. In the United States, different privacy laws have been passed for specific industries or situations. Some of these laws include the Children’s Online Privacy Protection Act (COPPA), the Health Insurance Portability and Accountability Act (HIPPA), the Electronic Communications Privacy Act (ECPA), and the Video Privacy Protection Act.[13]
Classification of Databases[edit | edit source]
Single-User vs. Multiuser Database Systems[edit | edit source]

Single-user database systems are located on one computer and they are designed for one user; often times, they are used for personal use and small businesses. Only one person can use the database at a time, so if one user is using the database the other users must wait until that user is done. While a multiuser database system is used for bigger businesses because it is a database that is accessed through a network. It is so more than one person can access and change the data in a system. Most use some kind of lock on the database so that there are no conflicts between people making changes. They can be on one computer or multiple computers.[14]
Client-Server and N-Tier Database Systems[edit | edit source]

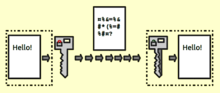
Most multiuser database systems are client-server database systems. Basically client-server database systems are servers that contain resources for other computers. It is when the client part, makes a service request from the server, which completes the request. For example a secretary using her PC (the client part) looks up the cost of a product on their system (ie on a server, not stored on her PC). The client is referred to as the front end and the database server is referred to as the back end.[15] Some of the client-server database systems have more than just the front end and the back end but also a middle part called a tier, which are referred to as n-tier database systems. In n-tier databases, the client and the database never communicate directly, all data is passed through the middle layer. The advantages of this database system is that the middle tier provides a layer of abstraction, that way you can change parts of the back end without having to modify parts of the front end. It is also a good way to separate responsibilities; they can also be more efficient.[16]
The Client Server Internet combinations gives IT another dimension to its organization. They first act like clients and servers of course, and they can access the internet as well to get into databases in distant locations. The final stage is to be able to create, view, use, modify, and delete applications as well as data. Software modules and hardware components are used to be able to actually perform functions. The client server connection are able to communicate with messages and these messages can be sent whether the server is online or off. The messages are sent through a network that may include both the intranet and internet. A network is a group of connected objects or people; the network is able to relay those messages to one another.
The main use for a client server is to produce a useful application for the business’s needs. Client servers use middleware which is an important part that allows for applications on the client end to be able to reach the actual network and talk to the server. It is the part that is in between the network and the application software. E-mails are a type of middleware since they are in between the network and the application.[17]
Centralized vs. Distributed Database Systems and Disk-Based vs. In-Memory Database Systems[edit | edit source]

Centralized database systems are all located on one computer. This can either be a server or mainframe computer. Distributed database systems share a network and the data is divided between several computers connected to that network.
An advantage of a centralized database system is that all information is in one place. The disadvantage may be that a bottleneck might occur. Having all information on one computer can make it easier to some users, but difficult for others who want to access the files. One advantage of distributed database systems is that the database can be accessed using any computer on the network even if all the information is not on one computer. This is the preferred type of system to use for databases, because information can be easily found. It also ensures that all data will not be lost, if using the distributed database system over the centralized system. Because of the recent advances in technology, using the “cloud” is another way to store database information over the Internet. This concept goes hand in hand with disk-based and in-memory database systems.
Most databases are stored on conventional hard drives in computers today, but recently many are switching to in-memory databases. This can hold all data on the main memory of the computer. This creates faster performances than it would if using the disk-based system.
In-Memory Database[edit | edit source]

An in-memory database (IMDB) is a database whose data is stored in main memory to facilitate faster response times.[18] In-memory databases are also sometimes referred to as main memory database systems, or MMDBs, and have become more popular in recent years for handing High-Performance Computing (HPC) and Big Data applications. Applications, such as those running telecommunications network equipment and mobile advertising networks, often use main-memory databases.
Three developments in recent years have made in-memory analytics increasingly feasible: 64-bit computing, multi-core servers and lower RAM prices.[19] The source is loaded into the system memory in a compressed, non-relational format. In-memory databases streamline the work involved in processing queries which provides faster and more predictable performance than from a disk (as access times and database requests are typically considerably faster when system memory is used as opposed to disk storage, particularly hard drive storage). Main memory databases are faster than disk-optimized databases since the internal optimization algorithms are simpler and execute fewer CPU instructions. Another advantage of in-memory databases comes into play when transactional data and analysis data is stored in the same database. It’s easier to carry out ad-hoc analysis as all of the data needed to analyze a business case is written to a single database.[20]
Database Models[edit | edit source]
Relational Database Model[edit | edit source]
Relational database management systems are important because they take several related tables and combine them in the least complex way that is possible. Essentially the RDBMS takes these smaller, less compact, tables and finds ways to relate them to one another based on singular variables to avoid repetition as much as possible. When creating such a database there are four main questions to ask: what is the point of this database? what information needs to be included in this database? which variables should be placed in which table to make the end result the least tangled/complicated? and how should this table be formatted? Once all those things are completed, one could use a program such as Microsoft Office's Access[21] to create a query by choosing specific related fields to display and organize. After this, one could use the query to generate a report which is essentially used to import the selected information into a singular database that would be easier to read through and find information from.

Relational database comes into play when an asset tracking database is needed, and spreadsheets are too large to use for the particular data. After the design of your new database, including the fields, data types, primary keys, and foreign keys, is finished, the next step is to actually go ahead and create the corresponding table for the database. The very first step to create a relational database is to create and name a new database file, which will contain all tables and objects included in the database. Next, using the table structure formed in the “design” phase of the process, each table in the database is created. And finally, once that table structure is complete, the last step is to enter the data into the tables, and relate different tables to each other as needed. In Microsoft Access, a table can be created under the Design View by entering each field name and specifying the data type and other properties as needed. However, if you wish to use your old or existing data in the new database, a process called data migration takes place by transferring the data from the old files to the new. Additionally, Design View also lets you make various sorts of edits in the form if you wish to have a specific layout or design—such as changing the form color, font size, the placement of the fields, or adding a heading, etc. [22]
Star Schema Model[edit | edit source]

Star schema is one of the simplest database models and is commonly used as a model for relational data warehouses and multidimensional databases. It consists entirely of fact tables and dimension tables. Fact tables are an event or entity such as a sale and a dimension table consists of details about that event such as date, place, speed of delivery, etc. For example, a geography dimension table can be used to describe location data, such as country, state, or city. In a star schema, a fact table is surrounded by numerous dimensions that branch out, creating an image similar to a star. One of the advantages of a star schema model is that it is compatible with Online Analytical Processing (OLAP) which allows for data mining of specific information from different points of view. For example, a user can view the sales from a specific item at any specific time in the past.[23] One of the disadvantages of the star schema model is that it is a simplistic model so it is not capable of creating complex relational analytics. Star schemas are also denormalized so it is possible for redundancies to occur within the database.[24]
Types of Relationships[edit | edit source]

There are three basic types of relationships among entities. These three types include: one-to-one, one-to-many, and many-to-many. In a one to one relationship every row in one table is linked to one specific row in another table. This means that there must be exactly as many rows in the first table as in the second table. This type of relationship isn’t very common due to the fact that there isn’t always a benefit to the design of a database. There is no benefit to the design because if the data is directly related it would make sense to have all the data in one table. One way that one-to-one relationships could be beneficial is if some of the data is needed, but isn’t used often. The data that isn’t used often could be stored separately, and away from the more important data.[25] One-to-many relationships allow each row in a table to be related to many rows in another table. This type of relationship is beneficial to a database due to the fact that you can reference frequently used data in many different tables by only entering it into one master table. Usually, the number of rows in the first table would be less than the number of rows in a second, third, forth, and so on, table. One-to-many relationships are often used in libraries. For example, names of authors in one table could correspond with the books each author has written in different tables.[26]
Hierarchical and Network Database Models[edit | edit source]

The hierarchical model is the oldest database models. It organizes data in a tree-like structure, using parent and child data segments. For example, it begins at the top of the tree with a single root. That stems into a lower level segment, which connects to other subordinate segments after. This is used to model one-to-many relationships. A disadvantage of using this model is that it requires data to be stored repetitively in multiple levels. This causes the database to function very slowly because it can be searching for information in lower levels as well. The network model uses a set structure. A set is comprised of an owner record type, a set name, and a member record type. This type of model shows many-to-many relationships. Parents can have multiple children, and children can have multiple parents. Both of these model types are outdated and no longer used for building new database applications. They are often less flexible than other model types. [27]
Also, all paths for accessing the data must be planned ahead of time and cannot easily be changed. Some places you might still see the hierarchical model might be in large systems that use high-volume transaction processing, like banks or insurance companies.
Object-Oriented Database Models[edit | edit source]

Whereas other database models can only store conventional data (such as dates, numbers, and text), the object-oriented database management system (OODBMS) is far more abstract. In an OODBMS, you can store pretty much any kind of data you desire, along with the methods to be used with that data. To retrieve this more complex and varied data, the user sends queries written in object query language(OQL) which is an object-oriented version of SQL. OODBMSs are becoming increasingly prevalent because of the higher demands of computer users today. However, as is the case with any new technology, there is some resistance because of the downsides of OODBMSs.

One downside is how editing an OODBMS based application is more time consuming because changes have to be made to the other classes in the application that interact with instances of the parent class, versus an RDBMS system where edits can typically be independent of the parent application.[28] This is very time consuming and that means a lot of money has to be spent on making changes to the object-oriented database management system. Many companies in the business world have certain budgets set aside for the information department, which includes the database system used for the company, and the OODBMS is very costly. Another disadvantage for the OODBMS is the lack of support for security and views. The user of an OOBDMS cannot grant individuals’ access to certain objects or classes within the system, which either means the individual wouldn’t be allowed to see the system at all or that they would get access to everything within the system, something businesses might not like. Also, the OOBDMSs do not contain a view mechanism, which is a disadvantage for employees who like to see their work and also to make sure everything they put in is correct. Two more disadvantages of OOBDMSs that go hand in hand is the lack of standards for the system and the fact that there is no universal data model. Without standards for the system, the cleanliness of the system can be dragged down and it could be hard to use. Many people like when something is universal because then they know what is right and wrong, something that cannot see with the OODBMS.[29] Even with the extra difficulties, many important clients continue to operate using a OODBMS, one big example being Chicago Stock Exchange, which uses the system to manage stock trades.

After looking at the types of database models, there are 4 steps involved with designing a relational database. The first step in designing a relational database is to identify the purpose of the database and the activities that it will be used for. These activities can range from keeping track of rental properties, students grades, customer orders, or inventory. Databases are used in a wide variety of ways and knowing what you will use your database for will help you create your database and optimize its use. In knowing what purpose your database will serve, you will be able to determine the data (fields) that needs to be included in the database, then the fields can be organized into tables. It is good to group fields that logically belong together. Next look at the table structure and ensure that all fields are represented and in the proper table. Look to see if there is any redundancy in the data, that way you can restructure fields in order to minimize that redundancy. Lastly, finalize the structure of each table, listing each field’s name, type, size and so on and selecting a primary key (data definition). This procedure will assist you in create a database that will suit your needs and provide the information you request.[30]
Databases on the Web[edit | edit source]
Web Databases in Use[edit | edit source]

There are many ways Web databases can be used. The most obvious way is the retrieval of information. Web databases provide a means for users to access the massive amount of information the Web has to offer, and this is made possible, in one way, by the use of search sites where databases provide links for the user. Other personal uses for databases include the storage of email addresses, telephone numbers, and other information for one who might create a site for friends and family.[31] On the business end, Web databases allow businesses to create “website polls, feedback forms, and client/customer inventory lists.”[32] This is a vital function that both large and small businesses can take advantage of to suite their needs. One, specific example relating to business-use of Web databases is the management of e-commerce-related activities. Here databases are used to provide information like pictures and pricing for products as well as order information and other necessary functions to enable efficient and reliable business transactions. Another feature of Web databases is their ability to display dynamic Web pages. These pages display information that changes depending on the input of the user, like a B2C site showing pages related to the interests of the consumer based on his or her past activities. From personal to business applications, Web databases are a vital part of addressing the tasks associated with Web-related activity.

Not only are websites becoming more and more personalized for the viewer, but the advertisements on the web page are as well. Companies including major search engine Google deliver targeted ads towards certain content and audiences. One method is contextual targeting, which analyzes keywords, word frequency, and link structures to determine what ads would match the content of the page. Placement targeting uses specific ads chosen by advertisers on certain web pages that are supposed to match what the viewer’s other interests may be and what other kinds of products they have to offer. Similar to this is interest-based advertising, which places advertisements relevant to certain interests on web pages that are commonly viewed by people with that similar interest. Google offers a program that people can use in order to set their interests so that ads are tailored towards their selections. Lastly, language targeting determines the primary language of the page and ensures that the advertisements shown will be in the same language. Advertisements would not work very well if the viewer could not even read what the product was that they were advertising! All of this information is placed into Google's ad search database which processes the information and ensures that the advertisement on your screen is going to be relevant to you.[33]
Middleware[edit | edit source]

This is a computer software that provides services to software applications beyond those available from the operating system. It is software that connects two otherwise separate applications, which can resemble "software glue.” For example, there are a number of middleware products that link a database system to a Web server. This provides the user to be able to receive data from the data base by using forms that are displayed on a Web browser, and it enables the Web server to return dynamic Web pages based on the user's requests and profile. As stated previously, the term middleware is used to describe separate products that serve as the glue between two applications. It is, therefore, distinct from import and export features that may be built into one of the applications. It is sometimes called plumbing because it connects two sides of an application and passes data between them. Distributed computing system middleware can loosely be divided into two categories. These categories are those who provide human-time services and those that perform in machine-time. This latter middleware is somewhat standardized through the Service Availability Forum and is commonly used in complex, embedded systems within telecom, defense and aerospace industries. [34]
How Web Databases Work[edit | edit source]

In our technological world, we use web-based database requests on a daily basis. We are constantly visiting web pages, clicking on links and using the menu to navigate us through our activity on that page. Using middleware, the web server passes a request on to a database query and the information is stored and passed along to the database server. The database server then uses this information to direct the page to where it was intended to go. CGI Script is another way information is passed along. They use instructions via a programming language and accept and return the websites data to the user. Active server pages are yet another example of scripts used commonly on websites. They are very similar to CGI Scripts, yet they are exclusive because they almost always use VBS script or Java script. PHP Hypertext processor is a language that is becoming more and more popular everyday. This script is extremely similar to CGI scripts and active server pages yet are more highly compatible with other programs. The script functions using PHP tags and html codes to get their job done. These scripts are just some examples of what is used today and how information in transmitted on a web server.[35]
CGI Scripts[edit | edit source]
A CGI (common gateway interface) script is a set of instructions written in a programming language (such as C, Perl, Java, or Visual Basic) and designed to accept data from and return data to a Web page visitor. On very busy sites, CGI can slow down server response time significantly because it processes each request individually. The usual placement of a CGI script is in the remote web servers cgi-bin directory, but the exact location of this directory is determined by the web administrator for that machine.[36]
Active Server Pages[edit | edit source]
Active Server Pages (ASPs), Microsoft's first server-side script engine for dynamically generated Web pages, have the extension .asp. ASPs work similarly to Web pages utilizing CGI scripts, but the code to tie the database to the Web site is typically written in JavaScript or VBScript. With simple HTML pages, the client requests a web page from a server. The server just sends the file to the client, and the page is shown on the client's browser. With Active Server Pages, the server gets a chance to alter the file before sending it to the user. To use Active Server pages you must be running a Microsoft web-server. If you are running a Microsoft Web server, to run an ASP file, all you need to do is create a file on the web-server with a .ASP extension. When the browser requests the file, the web-server is smart enough to preprocess the file before sending it off to the client.
PHP Scripts[edit | edit source]

PHP (PHP Hypertext Preprocessor) is a scripting language that is increasingly being used to create dynamic Web pages. Free to download and use,[37] It uses code similar to Perl or C++ that is inserted into the HTML code of a Web page using special PHP tags. Although PHP scripts perform tasks similar to CGI and ASPs, they have the advantage of high compatibility with many types of databases.
Review[edit | edit source]
Terms and definitions [38]
attribute A characteristic of an entity.
centralized database system A database system in which all of the data used by the system is located on a single computer.
client-server database system A database system where the database is located on a server and accessed by client devices.
collision an incident that happens when 2 or more records are assigned the same storage address.
column In a database, a field.
data definition The process of describing the properties of data that is to be included in a database table.
data dictionary The repository of all data definitions in a database.
data integrity The accuracy of data.
data privacy' Protecting the privacy of the data located in a database.
data security Protecting the data located in a database against destruction and misuse.
data validation The process of ensuring that data entered into a database is valid (matches the data definition).
database A collection of related data that is stored in a manner enabling information to be retrieved as needed; in a relational database, a collection of related tables.
database management system (DBMS) A type of software program used to create, maintain, and access databases.
direct organization A method of arranging data on a storage medium that uses hashing to specify the exact storage location.
distributed database system A database system in which the data used by the system is located on multiple computers that are connected via a network.
end-user database consist of data developed by individual end-users. Examples of these are collections of documents, spreadsheets, presentations, multimedia, and other files.
entity Something (such as a person, object, or event) that is important to a business or organization; typically becomes a database table in a database system for that business or organization.
field A single category of data to be stored in a database, such as customer names or employee telephone numbers. Also called a column.
form A formatted way of viewing and editing a table in a database. hashing algorithm a mathematical formula that finds where specific records are stored in the database.
hybrid XML/relational database A type of database system that can store and retrieve both XML data and relational data.
in-memory database (IMDB) A database that stores all data in memory instead of on a hard drive.
index A small table containing a primary key and the location of the record belonging to that key; used to locate records in a database.
indexed organization A method for organizing data on a storage medium or in a database that uses an index to specify the exact storage location.
metadata Data about data, such as the data contained in a data dictionary.
middleware Software used to connect two otherwise separate applications, such as a Web server and a database management system.
multidimensional database (MDDB) A type of database designed to be used with data warehousing.
multiuser database system A database designed to be accessed by multiple users.
normalization The process of evaluating and correcting the structure of a database table to minimize data redundancy.
object-oriented database management system (OODBMS)' A type of database system in which multiple types of data are stored as objects along with their related code.
primary key A specific field in a database table that uniquely identifies the records in that table.
query A request to see information from a database that matches specific criteria.
record A collection of related fields in a database. Also called a row.
relational database management system (RDBMS) A type of database system in which data is stored in tables related by common fields; the most widely used database model today.
report A formatted way of looking at information retrieved from a database table or the results of a query.
row In a database, a record.
single-user database system A database located on a single computer and designed to be accessed by a single user.
structured query language (SQL) A popular query language standard for information retrieval in relational databases.
table In a relational database, a collection of related records or rows.
Questions
Match each term with its example:
1.
A. When the database does not allow a user to enter a letter in a phone number field.
B. Requiring users to log on to a database system via a fingerprint reader.
C. Assigning a field the property of “required.”
i. Data definition
ii. Data integrity
iii. Data security
Fill in the blank
2. In a student information database, Name would be considered a(n) _______________, while all of Jennifer Mitchell's information would be a(n)___________.
3. Data _______ refers to accuracy of data.
4. When _____ organization is used, a hashing procedure determines where data is stored.
5. The term front end and back end refer to ______ database systems
True or False
6. Normalization is used to minimize data redundancy.
7. In a relational database, more than one table can be included in a database.
8. Using usernames and passwords is a data validation technique.
9. The network database model is the most widely used model today.
10. Dynamic Web pages commonly use databases.
Answers [39]
1. A. ii, B. iii., C. i.
2. field or column; row or record
3. integrity
4. direct
5. client-server
6. True
7. True
8. False
9. False
10. True
References[edit | edit source]
- ↑ http://www.usg.edu/galileo/skills/unit04/primer04_01.phtml
- ↑ http://ecomputernotes.com/fundamental/what-is-a-database/advantages-and-disadvantages-of-dbms
- ↑ http://products.office.com/en-us/excel
- ↑ https://support.office.com/en-us/article/Training-courses-for-Access-2013-a4bd10ea-d5f4-40c5-8b37-d254561f8bce?ui=en-US&rs=en-US&ad=US
- ↑ http://smallbusiness.chron.com/importance-inventory-databases-retail-40269.html
- ↑ Understanding Computers: Today and Tomorrow - 14th Edition Comprehensive
- ↑ http://www.mathsisfun.com/data/data.html
- ↑ https://docs.microsoft.com/en-us/sql/master-data-services/hierarchies-master-data-services
- ↑ http://ng.cengage.com/static/nb/ui/index.html?nbId=7345&nbNodeId=1013914#!&parentId=1013946
- ↑ https://docs.oracle.com/html/A96524_01/c05dicti.htm
- ↑ http://searchsoa.techtarget.com/definition/data-dictionary
- ↑ http://www-01.ibm.com/software/data/security-privacy/
- ↑ http://searchcio.techtarget.com/definition/data-privacy-information-privacy
- ↑ http://www.slideshare.net/raminder90/single-user-vs-multi-user-databases
- ↑ http://searchnetworking.techtarget.com/definition/client-server
- ↑ http://databases.about.com/od/specificproducts/a/architectures.htm
- ↑ http://www.networkcomputing.com/netdesign/1005part1a.html
- ↑ http://whatis.techtarget.com/definition/in-memory-database
- ↑ http://whatis.techtarget.com/definition/in-memory-database
- ↑ http://www.gft.com/etc/medialib/2009/downloads/techreports/2012.Par.0003.File.tmp/gft_techreport_inmemorydatabases.pdf
- ↑ http://office.microsoft.com/en-us/access-help/create-a-query-based-on-multiple-tables-HA010096275.aspx
- ↑ http://office.microsoft.com/en-us/access-help/create-tables-RZ101772997.aspx?section=2
- ↑ http://searchdatamanagement.techtarget.com/definition/OLAP
- ↑ http://searchdatamanagement.techtarget.com/definition/star-schema
- ↑ http://www.databaseprimer.com/pages/relationship_1to1/
- ↑ http://www.databaseprimer.com/pages/relationship_1tox/
- ↑ http://wps.prenhall.com/wps/media/objects/14071/14409392/Learning_Tracks/Ess10_CH05_LT3_Hierarchical_and_Network_Data_Models.pdf
- ↑ http://slashdot.org/story/01/05/03/1434242/why-arent-you-using-an-oodms
- ↑ http://www.scribd.com/doc/6142698/oodbms
- ↑ http://code.tutsplus.com/tutorials/relational-databases-for-dummies--net-30244
- ↑ http://www.htmlgoodies.com/primers/database/article.php/3478121/To-Use-or-Not-to-Use-a-Database-That-is-the-Question.htm
- ↑ http://www.ehow.com/info_8219542_database.html
- ↑ https://support.google.com/adsense/answer/9713?hl=en
- ↑ https://docs.djangoproject.com/en/1.3/topics/http/middleware/
- ↑ http://guide.netfronts.com/Database-PHP-ASP/adding_dynamic_web_content.html
- ↑ http://snowwhite.it.brighton.ac.uk/staff/mas/mas/courses/html/html3.html
- ↑ http://www.w3schools.com/php/php_intro.asp
- ↑ http://coursemate.cengage.com/CPReader/View/9781133114598/default.aspx?eISBN=9781133114598#66897dee-5c5a-4b7d-8a74-0eac7f4de56c
- ↑ http://ng.cengage.com/static/nb/ui/index.html?nbId=7345&nbNodeId=1013914#!&parentId=1013946
